
One Focus:
School Security
ACS’ sole purpose is to help you give every student, teacher, and administrator what they rightfully deserve: to feel safe on their campus.
Systems
We believe in innovative, technology-driven integration and maintenance tailored specifically to every school we work with.
- Access Control
- Intrusion Detection
- Fire Alarm
- Network Infrastructure
- Vape Detection
- Video Surveillance
Services

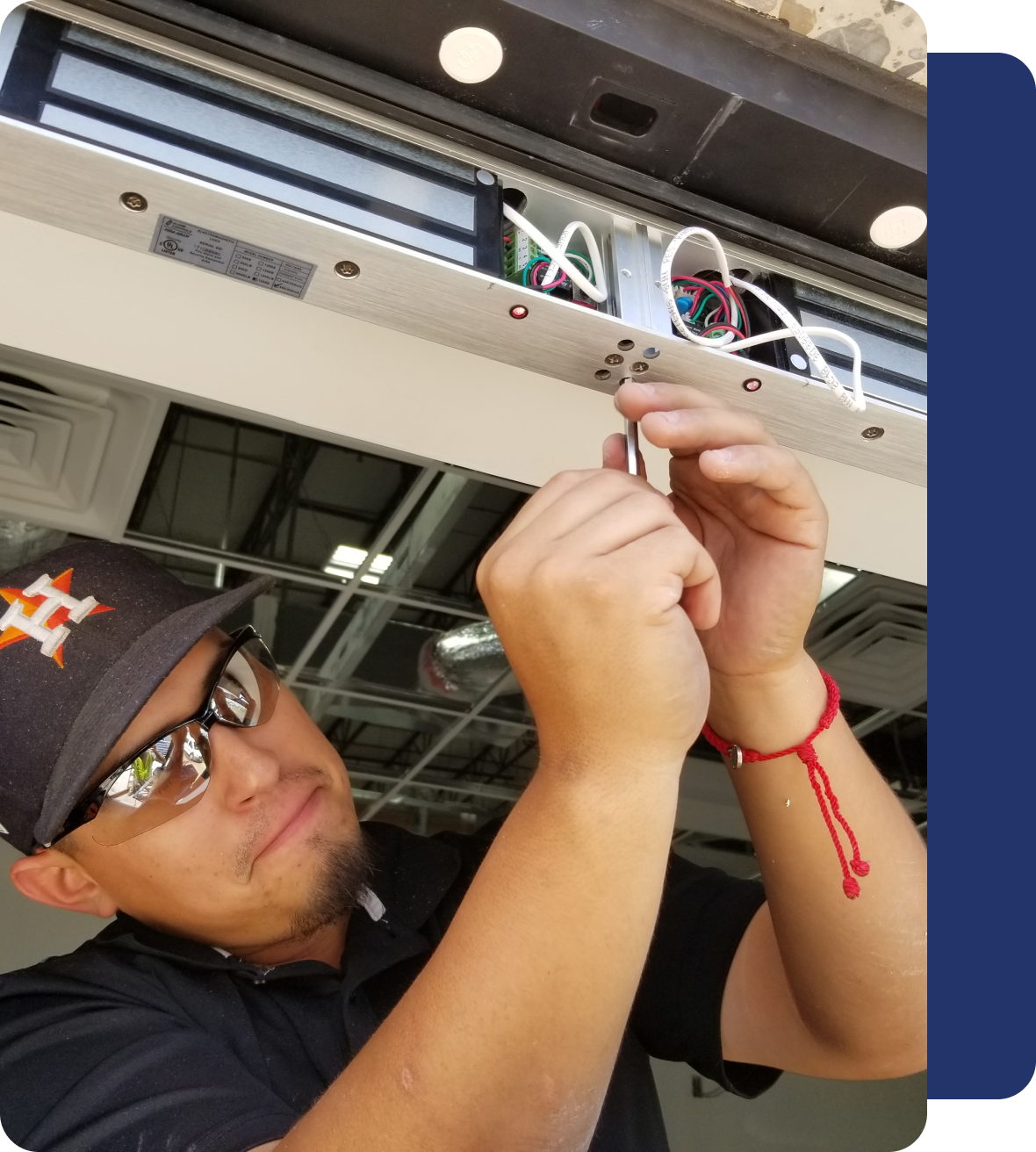
Installation
We provide organized and safe installation of our products that are designed to perform better in your surroundings.

Programming
We consider the needs of our client and their unique environment when programming their systems.

System Design
An outstanding system design that can never be tampered with or manipulated.

Needs Assessments
You can test our products and
pursue further to decide
about our services.

Troubleshooting
Our team is sharp enough to
support you with any errors
or issues regarding your
system.

Service Contracts
We offer customized service
contracts to provide fast
response teams to your unique
needs.

Remote Support
Many of our systems can be
supported remotely to
maximize the efficiency of the
onsite tech.

Inspections
We have designated inspection
teams to check the feasibility of
our products and installation.

System Testing
We keep updating our system
testing so you can trust our
products without concern.
Committed to Quality Products & Software
Having worked with over 500 schools across the country, we know that every campus is different. We guarantee to provide you with the right solution for your school.





The support team was extraordinary and consistently went the extra mile to help us with our installation.
I would highly recommend All Campus Security without hesitation.
I would highly recommend All Campus Security without hesitation.
John Smith | System Administrator, Peddie School

